Overview
Understanding Keycard's system architecture
Keycard is built on a distributed, cell-based architecture designed for security, scalability, and standards compliance.
Control Plane
Section titled “Control Plane”The control plane manages provisioning and orchestration:
- Zone creation and configuration
- Resource and application registration
- Organization and user management
- Cross-cell orchestration and monitoring
Data Plane
Section titled “Data Plane”Data planes are self-contained operational units that handle all runtime operations:
- OAuth 2.0 authorization flows
- Token issuance and validation
- Token exchange (RFC 8693)
- Credential encryption and storage
- Audit log generation
Key Benefit: Data planes operate independently without control plane dependencies. This architecture provides:
- High Availability: Cells continue operating even if the control plane is unavailable
- Reduced Blast Radius: Issues in one cell do not affect others
- Scalability: Add cells as demand grows without architectural changes
- Performance: Runtime operations avoid control plane latency
Learn more about deployment models →
System Components
Section titled “System Components”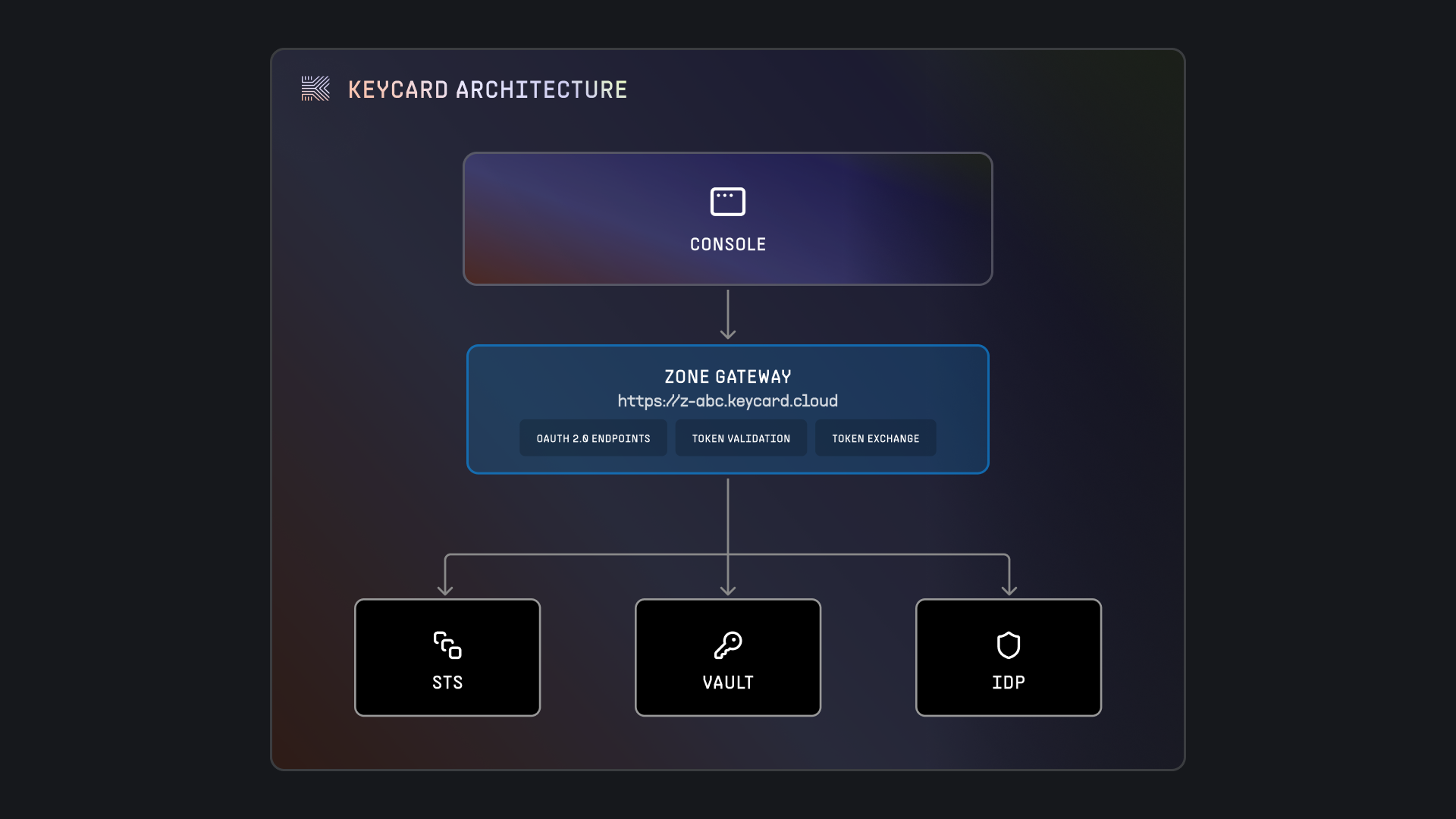
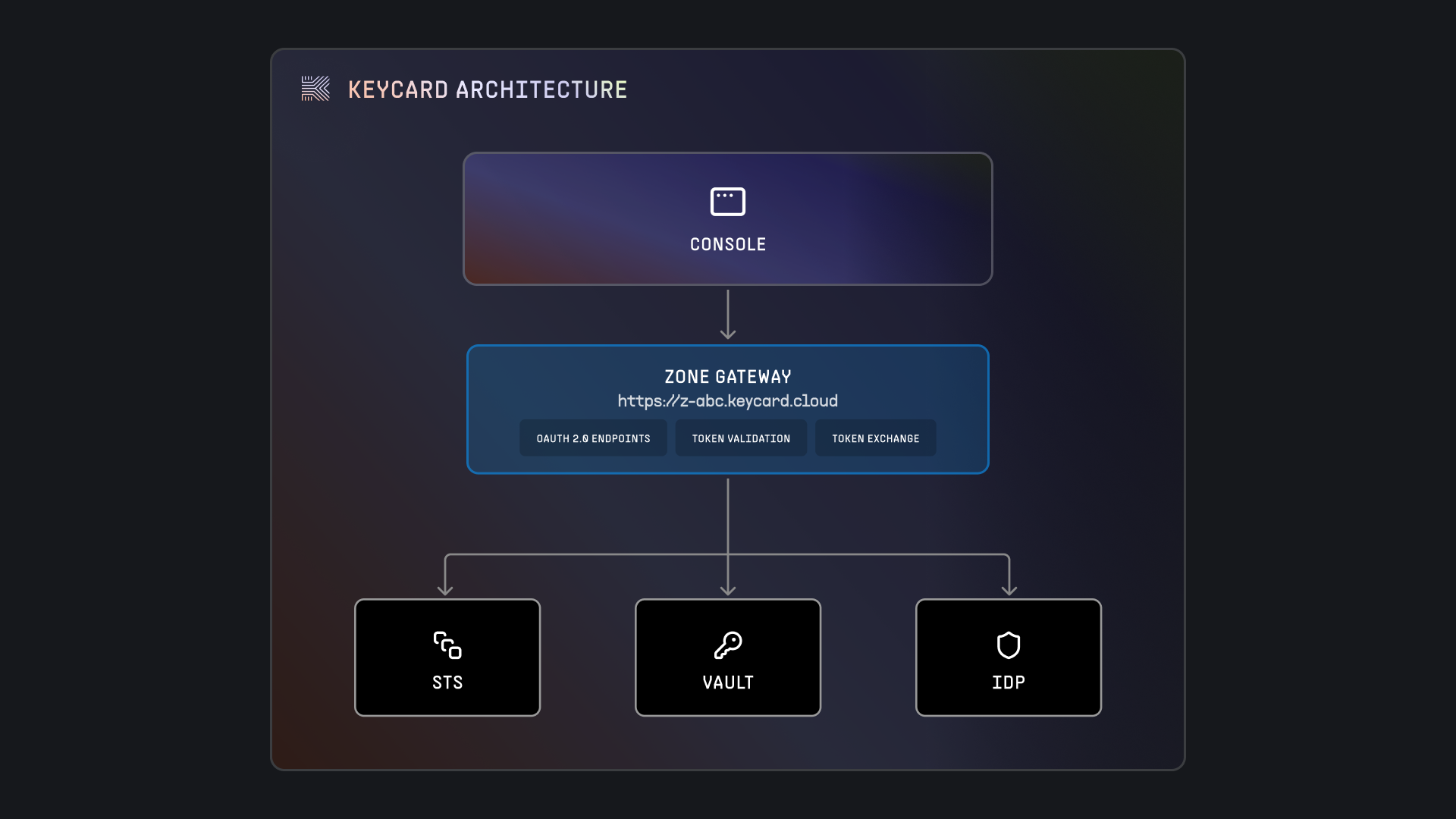
1. Keycard Console
Section titled “1. Keycard Console”Web-based management interface for:
- Configuring zones and identity providers
- Managing applications and resources
- Viewing audit logs
- Managing users and permissions
2. Zone Gateways
Section titled “2. Zone Gateways”Each zone has its own gateway endpoint:
https://<zone-id>.keycard.cloudGateways handle:
- OAuth 2.0 flows
- Token issuance and validation
- API requests for applications
3. Keycard STS (Security Token Service)
Section titled “3. Keycard STS (Security Token Service)”Core authentication and authorization service:
- Issues and validates JWT tokens
- Performs OAuth 2.0 token exchange (RFC 8693)
- Coordinates with external identity providers
- Manages session state
4. Keycard Vault
Section titled “4. Keycard Vault”Secure credential storage service:
- Encrypts API keys and secrets at rest
- Provides audited credential access
- Supports credential rotation
- Time-limited credential retrieval
5. Identity Provider (IdP)
Section titled “5. Identity Provider (IdP)”External authentication service configured per zone:
- Authenticates users via OAuth 2.0 / OpenID Connect
- Issues identity tokens to Keycard
- Supports any OIDC-compliant provider (Okta, Auth0, Google, Azure AD, etc.)
- Manages user identities and credentials
Standards Compliance
Section titled “Standards Compliance”Keycard implements industry standards:
- OAuth 2.0 (RFC 6749) - Authorization framework
- OpenID Connect - Identity layer on OAuth 2.0
- JWT (RFC 7519) - JSON Web Tokens
- RFC 8693 - OAuth 2.0 Token Exchange
- PKCE (RFC 7636) - Proof Key for Code Exchange
- JWKS (RFC 7517) - JSON Web Key Set
Authentication Flow
Section titled “Authentication Flow”See detailed authentication flow →